Trezor Login: Easy & Secure Crypto Access
Access your Trezor wallet effortlessly while keeping your private keys offline. Learn how to log in safely, confirm transactions securely, and manage your crypto assets with confidence.
What is Trezor Login?
Trezor login is the process of accessing your Trezor hardware wallet securely. It ensures your private keys remain offline, allowing you to send, receive, and manage cryptocurrencies safely.
Benefits of Using Trezor Login
- Private keys remain offline at all times
- Confirm transactions directly on the hardware device
- Supports multiple cryptocurrencies
- Integrates with Trezor Suite for portfolio tracking and analytics
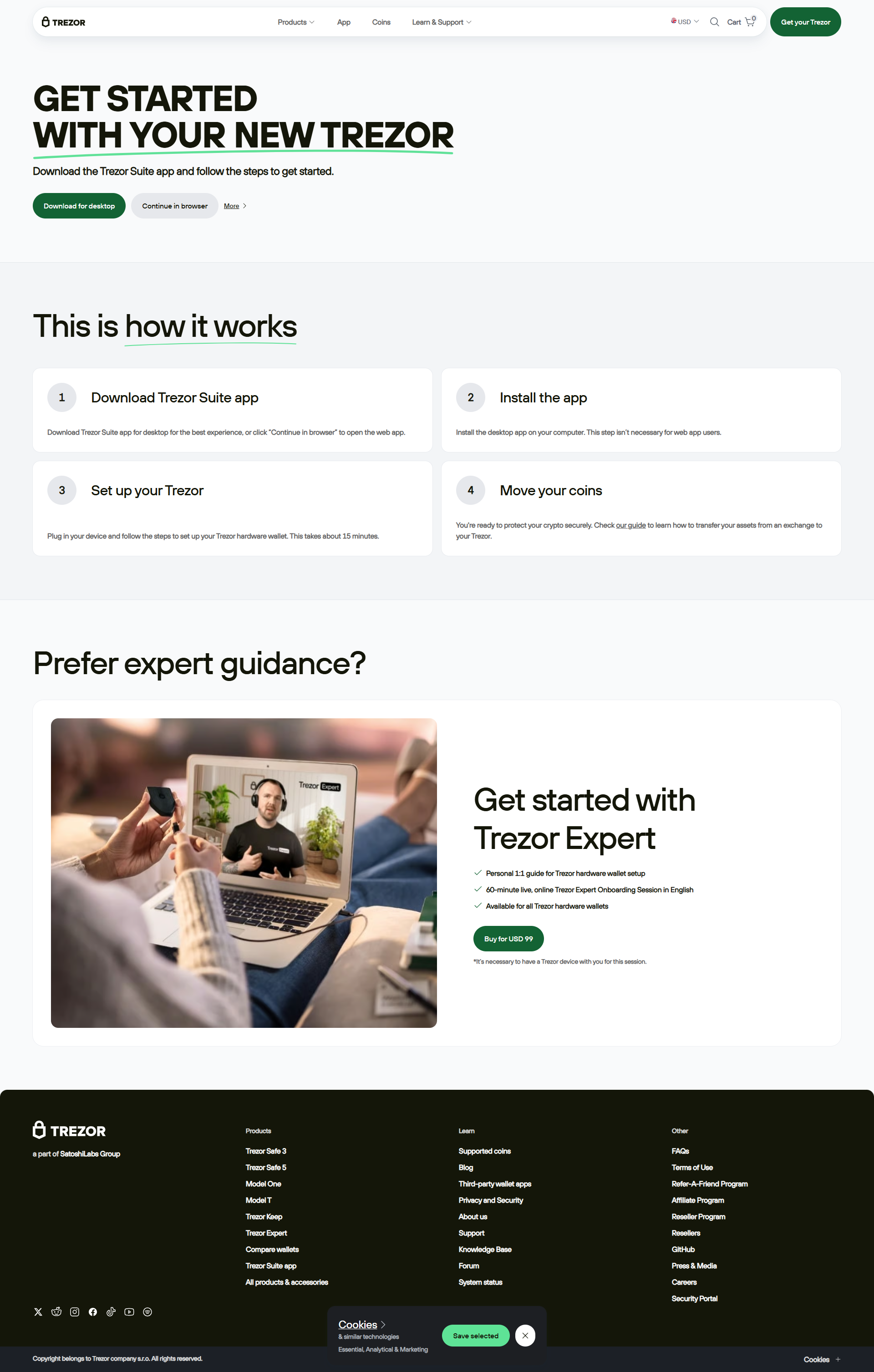
Step-by-Step Trezor Login Guide
- Connect Your Device: Plug in your Trezor using USB or supported connection.
- Open Trezor Suite: Launch the official desktop or web application.
- Enter Your PIN: Input securely on the hardware device.
- Access Wallet: View balances, send and receive crypto, and manage your assets.
- Confirm Transactions: Always approve actions directly on the device.
- Log Out: Close the Suite and disconnect your device safely.
🔐 Security Reminder
Always use official Trezor Suite software or verified web apps. Never share your recovery phrase online and confirm all transactions directly on your Trezor device.
Trezor Login vs Third-Party Access
| Feature | Official Trezor Login | Third-Party Apps |
|---|---|---|
| Security | Private keys offline; PIN required | Higher risk of phishing or malware |
| Authenticity | Verified through Trezor Suite | Potentially unsafe platforms |
| Ease of Use | User-friendly with guided steps | Varies, may cause errors |
| Recommended Users | All Trezor users | Experienced users only |
Troubleshooting Trezor Login
Device Not Detected
Reconnect the device, restart Trezor Suite, and ensure firmware is updated.
Forgot PIN
Reset the device using your recovery phrase and set a new PIN.
Suite Loading Problems
Restart your computer, close conflicting apps, and ensure the latest Trezor Suite is installed.
Trezor Login Checklist
- ✅ Connect your Trezor device
- ✅ Open official Trezor Suite
- ✅ Enter PIN securely
- ✅ Manage crypto safely
- ✅ Log out and disconnect after use
Conclusion
Using Trezor login through official methods provides maximum security for your cryptocurrencies. By confirming transactions on the device and following best practices, you maintain full control over your digital assets with confidence.